TimThumb, a small php script to resize and crop images on the fly which being use by many WordPress themes (usually premium WordPress themes such as elegantthemes) all over the net. This script has been compromised with zero day vulnerability. This blog and my other blog which using TimThumb also being hacked and injected with some malicious code to the WordPress core.
The compromised script was TimThumb v2.7 and below. If you are using that script, YOU MUST UPDATE IT NOW!!! I spent 3 hours to cleaning up my WordPress blog since the attacker injected their code to many location.
TimThumb Zero Day Vulnerability Symptoms
How the attacker inject their code may be vary to each one of you. But in this blog they inject their malicious code to my jquery.js, iI10n.js and put a shell code in wp-contents folder so they can get in and out easily. Their code may be encrypted so it is harder to find it, you can see the screenshots below:
![]()
This code is in I10n.js
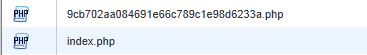
This code is injected code int TimThumb cache folder
Those code only show ads on my blog, which is annoying. But the attacker could do worse than that by injecting shell code so they can do anything to your website and database. And worst they can control your server. So i remind you please update your TimThumb script now!
TimThumb Zero Day Vulnerability Recovery
So now you know that you got hacked and injected with some malicious code. What to do now? Here some little steps to cleaning up your WordPress blog:
- First, BACKUP YOUR DATABASE! It is a must.
- Replace all files wp-admin and wp-includes folder from the WordPress official website. If you have done some changes to WordPress core, please merge your code as you can.
- Delete all files in cache and tmp folders.
- Delete all files in timthumb cache folders.
- Get the latest TimThumb script and overwrite your TimThumb script.
- If you have shell access you can find all the malicious code by using this command: “grep -r base64_decode *” and find the last 10 days modified script under wp-content folder with this command: “find /path/to/wp-content -mtime 10” and check if the files is injected.
- Update your WordPress plugins, the attacker may be injected some code to your plugins as well.
- Find php code in the uploads folder, there shouldn’t any php files under upload, tmp and cache folder. And delete it.
- Consult with your hosting security support and tell them to check and scan your website.
That would be most of it, but to be sure download your access_log and see if there are any malicious request to your blog. Get the attackers ip and ban it from .htaccess.
TimThumb Zero Day Vulnerability Sources
Mark Maunder (WordThumb author) announcement: He announce the zero day vulnerability in may wordpress themes, and also he and Ben Gillbanks (TimThumb author) worked together to rewrite all the TimThumb script and merge it with WordThumb.
TimThumb 2.0 by Ben Gillbanks.
WordPress FAQ what to do when you got hacked.
PS: If you need my help to clean up your website from malicios code, please leave me any comment below or use the contact form. Thanks.
OK, one of my blog was hacked, bet there is 100.. of IP – its imposible to ban them all.